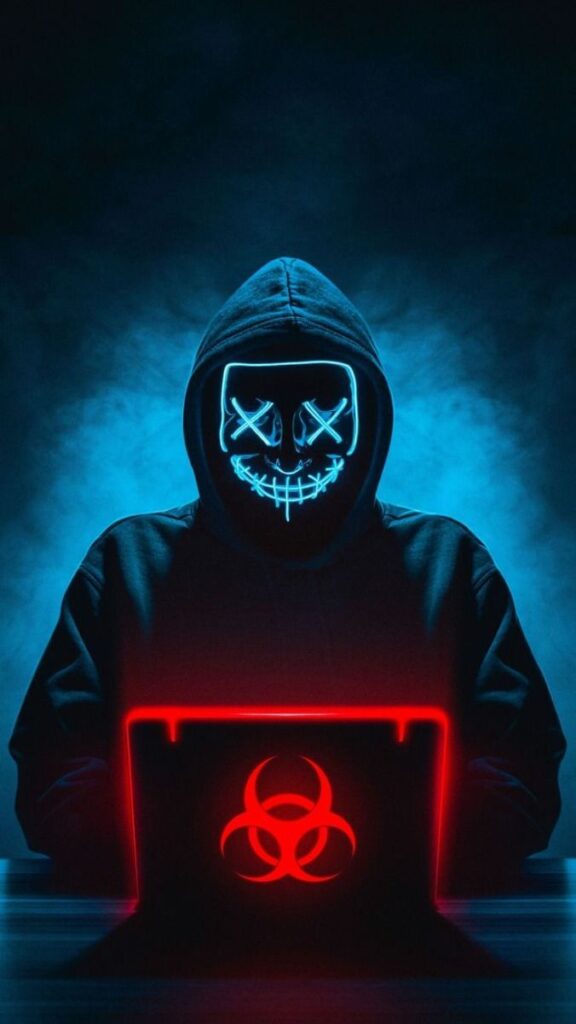
In the digital age, face hackers have become symbols of mystery, anonymity, and cyber intrusion. Often depicted in dark hoodies, glowing screens, and featureless masks, they represent the silent operators navigating the complex world of the internet. Face hackers are not just limited to fiction or movies; they embody a real phenomenon of individuals who exploit vulnerabilities in networks, systems, or personal data. Their appearance, often inspired by pop culture like Guy Fawkes masks or glitchy digital visuals, evokes both curiosity and fear.
The aesthetic of the face hacker—dark, eerie, and enigmatic—highlights their connection to the digital underworld. They stand at the crossroads of cybersecurity, activism, and sometimes malicious intent. From hacking into corporate servers to championing cyber freedom and privacy, face hackers reflect the power and dangers of the internet. Their image continues to evolve, making them a recognizable yet elusive figure in modern storytelling and cyber culture.
#1

Face hackers symbolize anonymity and rebellion, often hiding behind digital masks to remain unidentified.
#2

The Guy Fawkes mask became synonymous with hacker culture due to its connection with “V for Vendetta” and groups like Anonymous.
#3
These individuals often work in the shadows of the internet, breaching systems for personal, ethical, or political reasons.
#4

Face hackers are depicted wearing hoodies and masks to embody their mysterious and elusive presence.
#5

Their glowing screens and dark environments emphasize their connection to advanced digital operations.
#6

Some hackers fight for justice through ethical hacking, exposing corruption and championing digital rights.
#7

The term “hacktivist” describes hackers who use their skills for activism, supporting causes like freedom of speech.
#8

Cyber criminals, however, use hacking techniques for theft, extortion, and malicious attacks against individuals or companies.
#9

The rise of data breaches highlights the increasing role hackers play in the fight for digital information security.
#10

Hollywood movies and TV shows often glamorize face hackers as cyber geniuses who solve impossible problems.
#11

These figures blur the lines between heroes and villains, depending on their intent and actions in the cyber world.
#12

Cyber masks whether physical or digital symbolize the protection of identity and freedom from surveillance.
#13

Face hackers often exploit weak systems or loopholes to highlight vulnerabilities, forcing companies to improve security.
#14

Their use of neon, glitch effects, and dark aesthetics reflects the chaotic nature of digital breaches.
#15
Anonymous, one of the most well-known hacking collectives, brought face hackers into mainstream awareness.
#16

Some face hackers are whistleblowers who expose unethical practices, creating controversy and sparking debates.
#17

The hoodie-and-mask appearance serves as a cultural archetype for rebellion and digital resistance.
#18
The hacking community operates on forums, dark web spaces, and encrypted networks to maintain secrecy.

I’m interested in the creating sofisticated cybersecurity providing the right to emphasise the same value of the comfort provided to me and to every cyberpunk team Mainnet pilot member who is growing to retention respect of elevated heavy carried Independent
IDENTITY which should never have been spectacularized.